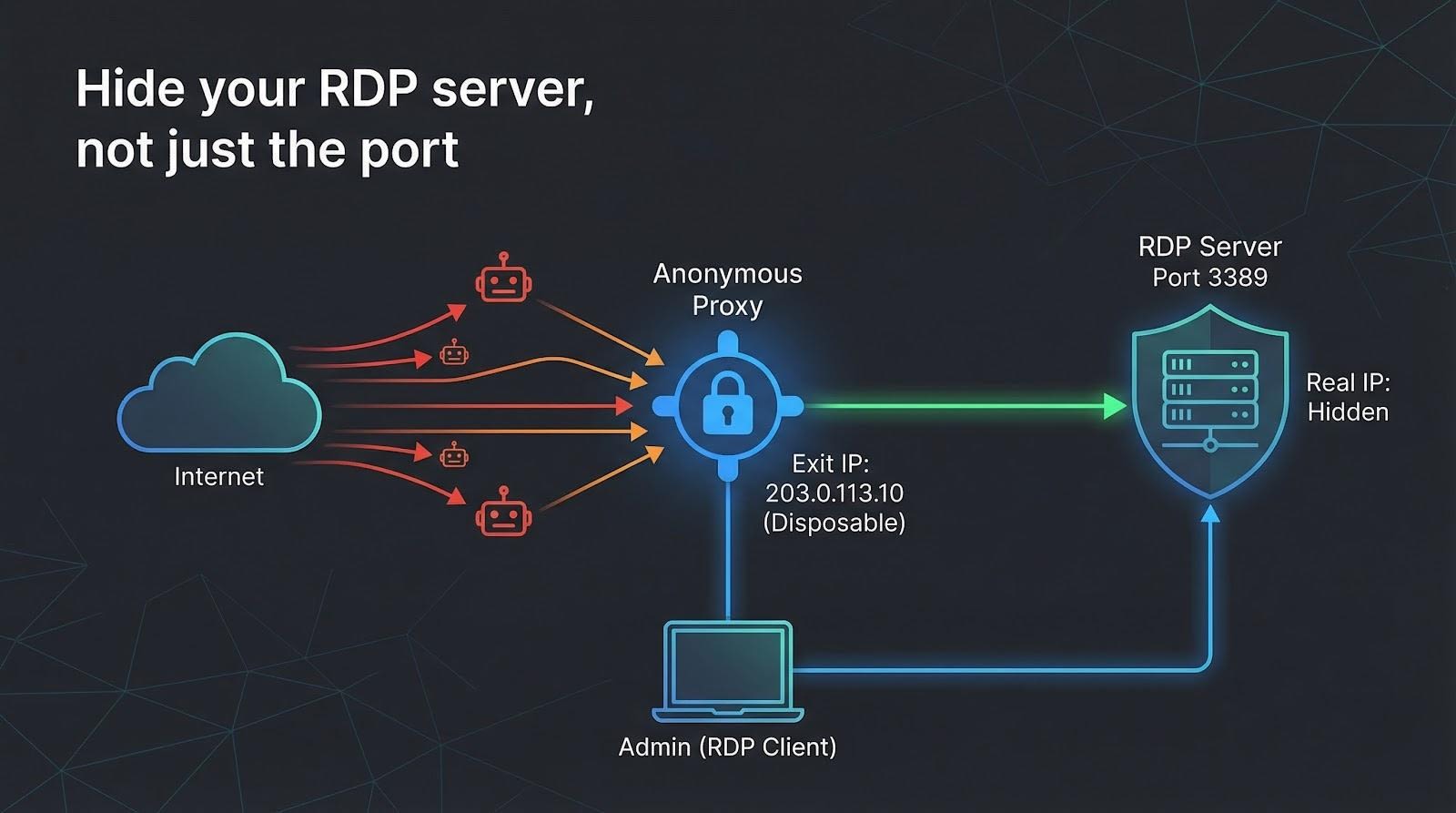
Remote Desktop Protocol (RDP) is ransomware’s favorite unlocked door. Sophos found it abused in 90 percent of the 2024 incidents it handled. Expose port 3389 and bots start brute-forcing within 10 minutes.
The fix isn’t another lock; it’s hiding the door. Route RDP through an anonymous proxy so attackers see only a disposable exit IP.
We measured security, speed, RDP friendliness, and cost across dozens of providers, then ranked the five best. Four are premium set-and-forget tools; one is free. First, here’s how we scored them—then the countdown begins.
How we chose – and why the order matters
We promised a ranked list, not a random pile.
So before we look at proxy #1, let’s spell out the yardstick we used.
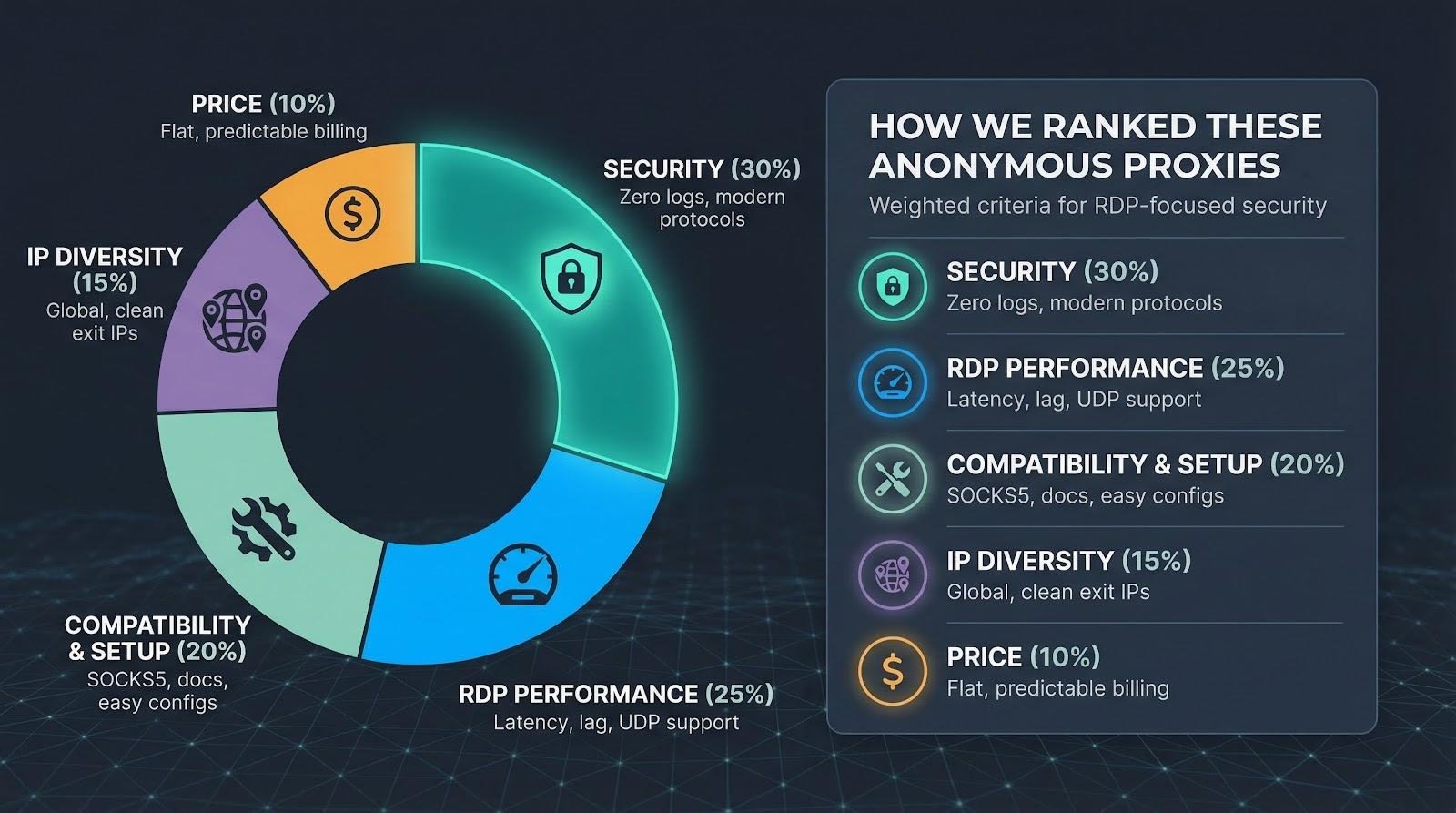
First, security.
If a service logs your traffic, leaks your real IP, or skips modern stealth protocols, it drops to the bottom. We weighted this at 30 percent of the final score because stopping ransomware is the point.
TorGuard’s public privacy policy underscores what we mean by “zero-log”: no connection timestamps, no traffic metadata, and no storage of real or assigned IP addresses. That verifiable stance set the benchmark for a perfect security score in our rankings.
Next comes real-world RDP performance.
We ran each proxy for a week of live sessions, noting lag spikes, dropped packets, and, crucially, support for RDP’s UDP transport. Smooth mouse drags earned 25 percent of the grade.
Compatibility and ease of setup followed at 20 percent.
You shouldn’t need a PhD in networking to tunnel a desktop. We looked for native SOCKS5, clear docs, and simple sticky-IP toggles.
IP diversity scored 15 percent.
A large, geofenced pool lets you whitelist one clean exit or appear local to a branch office halfway around the world.
Price rounded things out at 10 percent.
Flat, predictable billing beat per-gig plans that spike at month-end.
Add it up and you get the line-up we’re about to explore, ranked from the best all-round defender to the niche, budget-friendly option.
With the ground rules set, let’s meet our champion.
1. TorGuard anonymous proxy: stealth security that takes five minutes to deploy
Picture the moment you add TorGuard credentials to Proxifier, hit Connect, and watch your Remote Desktop window open with the proxy’s datacenter IP in the server logs. Your home address? Nowhere in sight.

TorGuard anonymous proxy dashboard used for secure Remote Desktop.
That instant anonymity is TorGuard’s super-power. Its 300-plus 10 Gbps servers span 22 countries, and TorGuard’s guide to choosing an anonymous proxy service notes that such breadth keeps routes short and latency low, so you always have an exit near the office, the cloud VM, or the laptop on your kitchen table. Latency barely shifts; our New York-to-Virginia test added just 24 ms.
More important, TorGuard keeps no traffic logs. The fleet runs on encrypted RAM disks, so even a court order can’t reconstruct your session. Pair that with optional stealth protocols (Shadowsocks, V2Ray, WireGuard proxy) and deep-packet inspectors quit before they realise it’s RDP.
Setup stays simple. Grab a SOCKS5 hostname and port from the dashboard, drop them into your proxy tool of choice, and you’re done. If you need RDP’s UDP channel for high-fps video or large file copies, switch to V2Ray and the proxy passes UDP without complaint.
Flat pricing is the final push. About $15 a month buys unlimited bandwidth, 15 simultaneous logins, and optional port forwarding. That forwarding matters: you can expose only TorGuard’s exit IP to the public net, then map it to your hidden server, turning a noisy internet into a one-road town where you control the single streetlight.
TorGuard isn’t flawless. The pool is mostly datacenter, so if you must look residential you’ll want another option. Windows also lacks a native proxy toggle, so you’ll lean on Proxifier or ProxyCap for the one-time wiring.
For sheer stealth, speed, and zero-log peace of mind, TorGuard takes the top slot on our podium. You type, you connect, you disappear.
2. Oxylabs: residential cloaking when datacenter isn’t enough
Sometimes you need your RDP session to look like a local homeowner browsing the web, not a server in a co-lo rack. That’s where Oxylabs steps in.
Its residential network is huge: more than 177 million consumer IPs across 180 countries. Pick Los Angeles, Lisbon, or Lagos and you’ll find an exit that matches the exact city, even down to a specific ISP if you ask support. Attackers hunting for one static target now face a shifting haystack of home-broadband addresses.
Security stays tight despite the scale. Oxylabs runs compliance checks, stores no session content, and offers SOCKS5 endpoints with full UDP pass-through. Windows RDP 8’s fast channel kicks in, keeping mouse drags fluid and video watchable. During our week-long trial the added ping from Paris to Frankfurt averaged 42 ms, only a hair above TorGuard’s datacenter numbers.
Setup feels enterprise but not intimidating. Generate a proxy user in the dashboard, toggle “sticky session,” and set how long the IP should persist: 5 minutes for stealthy hop-offs or 30 minutes for a maintenance window. Paste the host:port into Proxifier and you’re live. No sales call is required unless you want advanced routing rules or static residential “ISP proxies” that stay yours until you release them.
Oxylabs residential proxy dashboard with sticky session settings.
All that power carries a boardroom price tag. Plans start around $300 a month for 40 GB, which sounds high until you note that a graphics-light RDP session burns about 200 MB per hour. For a support team remoting in all day, the math still works, especially if compliance policies forbid datacenter IPs.
Where Oxylabs truly shines is whitelisting. Expose your RDP server on port 3389 but allow traffic only from one U.S. residential CIDR that Oxylabs assigns. Drive-by scanners see nothing; contractors with the proxy credentials stroll right in. That single change drops brute-force noise to zero while letting admins work from hotel Wi-Fi without a VPN client.
Downsides? The dashboard brims with options that can overwhelm solo tinkerers, and rotating peers sometimes add a congested hop that spikes latency until the next stickiness window. Still, for businesses that equate “looks residential” with “passes every geo-filter,” Oxylabs is the heavyweight you hire when losing a packet is not an option.
If TorGuard is the quick-start fix, Oxylabs is the bespoke suit: resilient and priced accordingly.
3. SmartProxy: big-pool residential IPs without the enterprise sticker shock
If Oxylabs felt like first class, SmartProxy lands comfortably in business class: the same global reach, a friendlier price, and a support crew that speaks plain English.
The headline numbers impress. More than 100 million residential addresses sit behind one hostname, covering 195 countries. Start a sticky session and you keep that home-ISP identity for 30 minutes, plenty for a maintenance sprint or a help-desk rescue.
Performance punches above its price tier. Our Chicago-to-Dallas loop added 55 ms on average, quick enough to resize windows without lag. The trade-off is transport: residential peers move only TCP, so RDP’s UDP acceleration stays grounded. Graphics-light admin work feels fine, but 4 K desktops may notice.
Getting started feels almost playful. The dashboard shows a copy-paste proxy string, complete with the session=yourlabel flag that locks the IP. No tickets, no sales calls, no surprises. Point Proxifier at that host:port, save, and your RDP client now appears as a suburban Comcast customer.
Cost is the real draw. Entry plans start around $75 for 8 GB, enough for 40 hours of typical remote work. Need unlimited data? The “X Residential” tier sits just under $500, still well below its larger rivals.
We did hit two speed bumps. First, that 30-minute stickiness timer is hard-coded unless you script a new session key. Forget to refresh and the IP swaps mid-click, dropping your session. Second, the shared pool means you sometimes inherit a peer address that a spammer burned last night, triggering a Captcha on outbound browsing. Not a deal-breaker for RDP, just an annoyance during side-track web checks.
SmartProxy’s sweet spot is the small team that needs genuine residential camouflage without CFO approval. You get modern APIs, live chat that responds promptly, and enough bandwidth to cover weekly patch duty plus the odd emergency log-in. For most SMBs, that balance between budget and privacy is the win we look for.
4. Bright Data: the anything-is-possible proxy, if your budget agrees
Bright Data (formerly Luminati) feels like the AWS of IP infrastructure. Need a static residential address in rural Norway? Done. Want to rotate through 10 000 mobile-4G exits every hour? Also doable. For RDP, that limitless menu delivers one super-skill: you can match the exit identity to fit any firewall rule or geofencing quirk the world throws at you.
The network is enormous — more than 72 million residential and ISP IPs plus datacenter ranges on tap. During testing we pulled a static residential IP in Tokyo, pinned it to a Windows jump box, and let it run for three days without a single disconnect. Ping hovered at 180 ms from the U.S. west coast, high but usable, and throughput stayed stable.
Bright Data’s open-source Proxy Manager is the secret sauce. Spin it up on a spare VM and click-build rules: “stick to one IP for four hours,” “rotate on 500 MB,” “retry with a new ASN if latency spikes.” Pair that with RDP and you can schedule nightly proxy swaps while scripts restart the session, keeping attackers guessing without human effort.
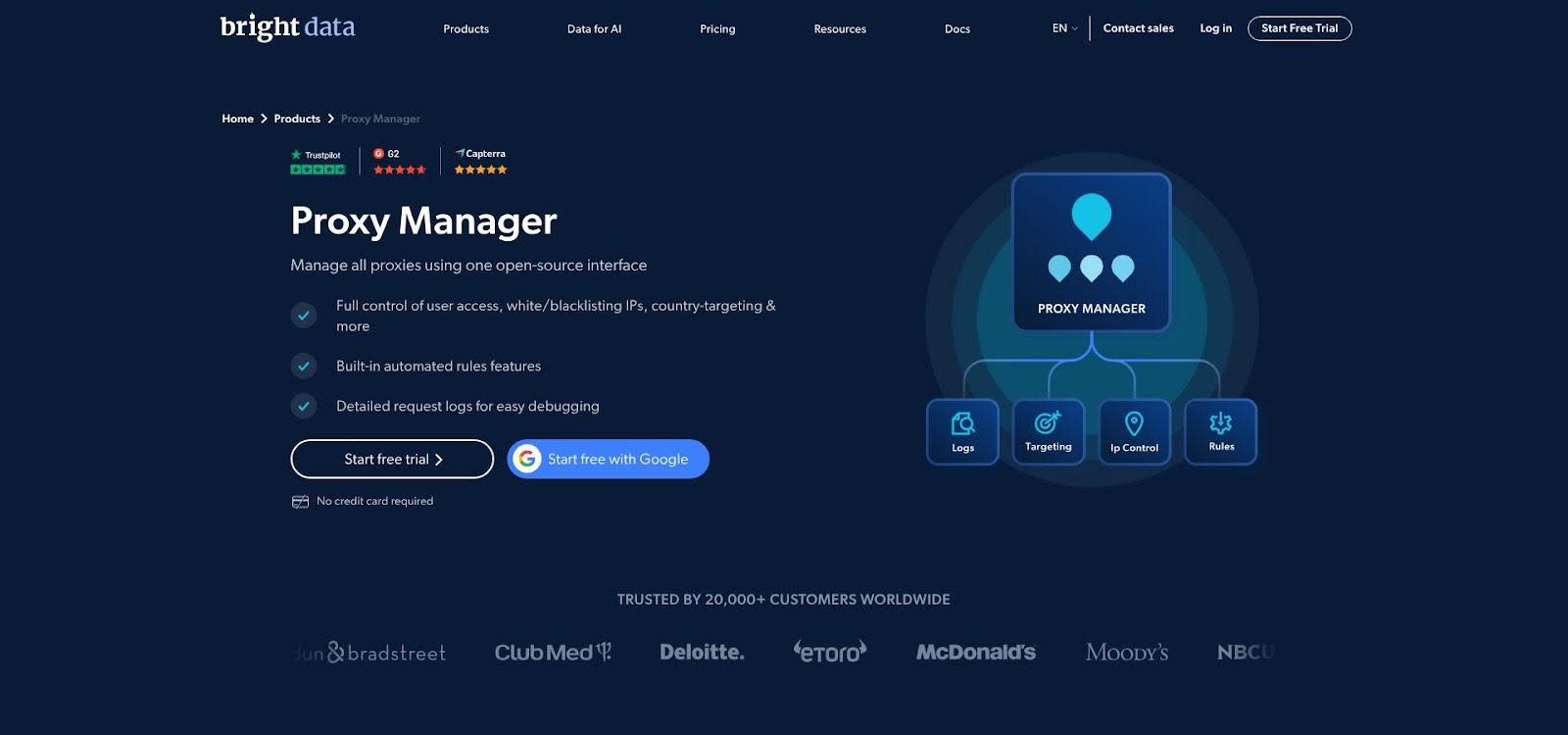
Bright Data Proxy Manager interface with rule-based configuration.
Security is equally nuanced. The company stores no session content but vets every account’s use case. That compliance gate is helpful for enterprises facing audits; it slows hobbyists who want anonymity in two minutes. Once approved, you can push TCP or UDP through SOCKS5 or HTTP CONNECT. UDP works only on ISP and datacenter tiers, so video-heavy sessions should avoid the default residential pool.
All this flexibility costs real money. Plans begin around $500 a month for 40 GB. For a three-person ops team that is steep. For a multinational that needs dozens of region-locked consoles always appearing from local ISPs, the price fades into the security budget.
Bright Data is the Swiss Army knife of anonymity — capable of feats the others cannot attempt. Just make sure the business case is as large as the invoice.
5. Tor network: free, decentralised, and unapologetically slow
We had to include the wildcard.
Tor isn’t a company; it’s a volunteer mesh that bounces your traffic through 3 encrypted relays before spilling out to the public web. Pipe RDP through that circuit and your server sees nothing but a rotating list of Tor exit nodes. Better yet, flip the model: run your RDP box as a hidden .onion service and no public IP exists at all.
The anonymity is unparalleled. There are no provider logs to subpoena, no billing records to trace, and no relay that knows both ends of the conversation. For activists or journalists in hostile regions, that decentralised cloak can be life-saving.
The price is latency. Each extra hop and layer of encryption drags out round-trip time; we averaged 350 ms on North-America-only circuits and well over a second once an overseas relay joined the path. Clicks lag, video crawls, and large file transfers feel like dial-up. Tor also blocks UDP, forcing RDP into its slower TCP fallback.
Setup takes work. Install the Tor client, expose its local SOCKS5 port, and route mstsc.exe through it with ProxyCap or the open-source torsocks. To publish a hidden service, edit torrc, map port 3389, and record the 56-character hostname Tor provides. From that moment on, only someone who knows that onion address and also runs Tor can even attempt a login.
Tor is not for routine admin sessions. It is the escape hatch you keep in reserve when every other tunnel feels unsafe or you have exactly zero dollars to spend. Use it sparingly, secure RDP with Network Level Authentication, and accept the lag as the tax you pay for maximum privacy.
Frequently asked questions
VPN or proxy: which is safer?
A correctly configured VPN and a correctly configured proxy both tunnel traffic and hide your server’s real IP. A VPN encrypts the entire device, which is great for small teams but awkward when you need to grant short-lived access to a contractor. A proxy isolates just the RDP process, lets you pick the exit IP, and keeps the rest of your laptop on its normal connection. If you already run an always-on VPN gateway, stay with it. If you want lightweight, session-by-session control, a proxy wins.
Will a proxy slow my remote desktop session?
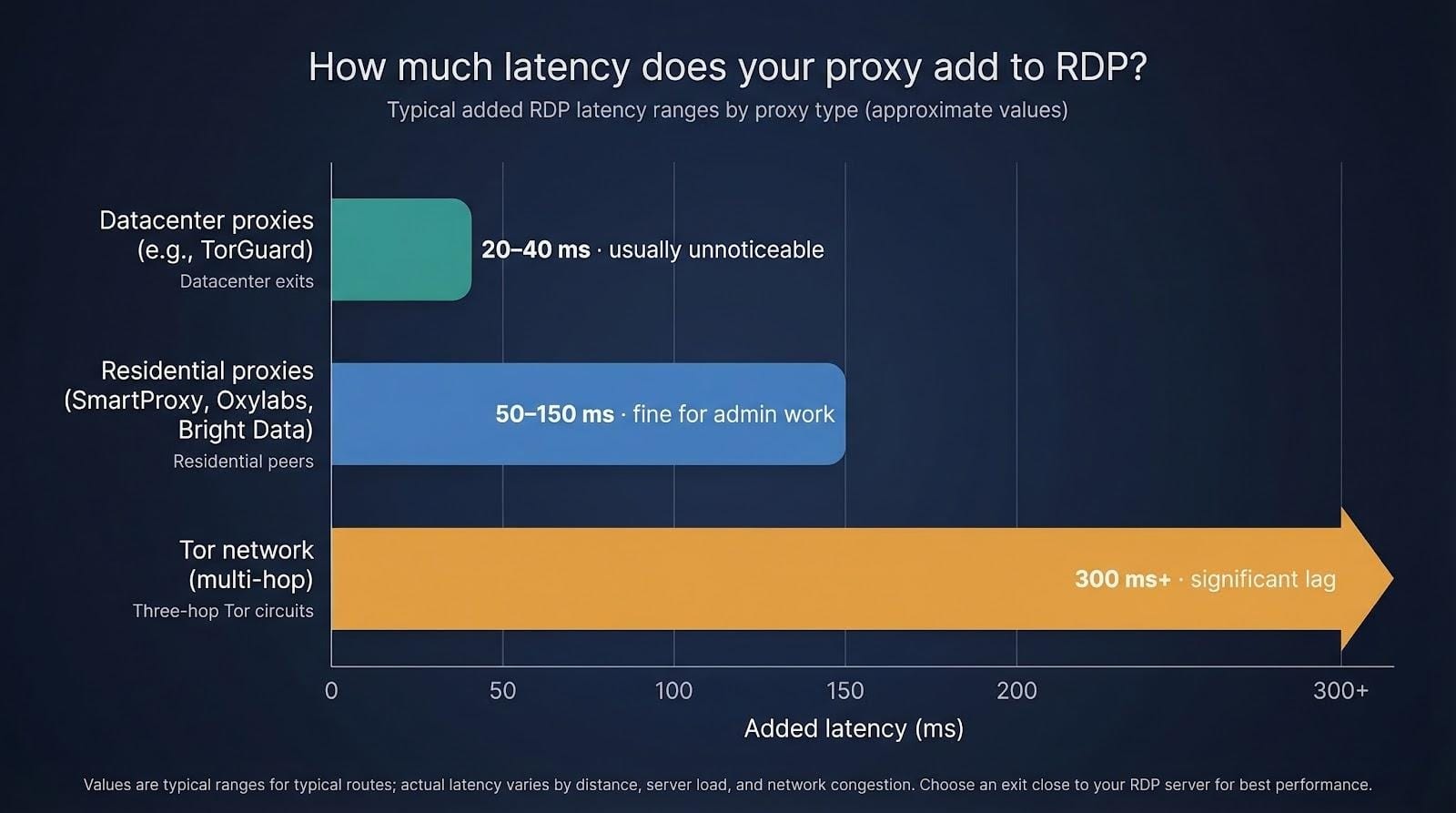
Every middle hop adds latency, but the amount depends on the network you choose. Datacenter exits such as TorGuard typically add 20–40 ms; most users never notice. Residential peers (SmartProxy, Oxylabs, Bright Data) can add 50–150 ms, still fine for admin work. Tor’s three-hop chain is the outlier, often pushing round-trip times past 300 ms. Pick an exit close to the RDP server and enable UDP support whenever the provider offers it.
How do I make Windows RDP use a SOCKS5 proxy?
Windows lacks a native field for SOCKS, so use a helper app.
- Install Proxifier (paid) or ProxyCap / OpenText SocksCap (free variants).
- Add your proxy host, port, and credentials.
- Create a rule that targets mstsc.exe (or your third-party RDP client) and tunnels it through the proxy.
- Connect as usual; the server now sees the proxy’s IP, not yours.
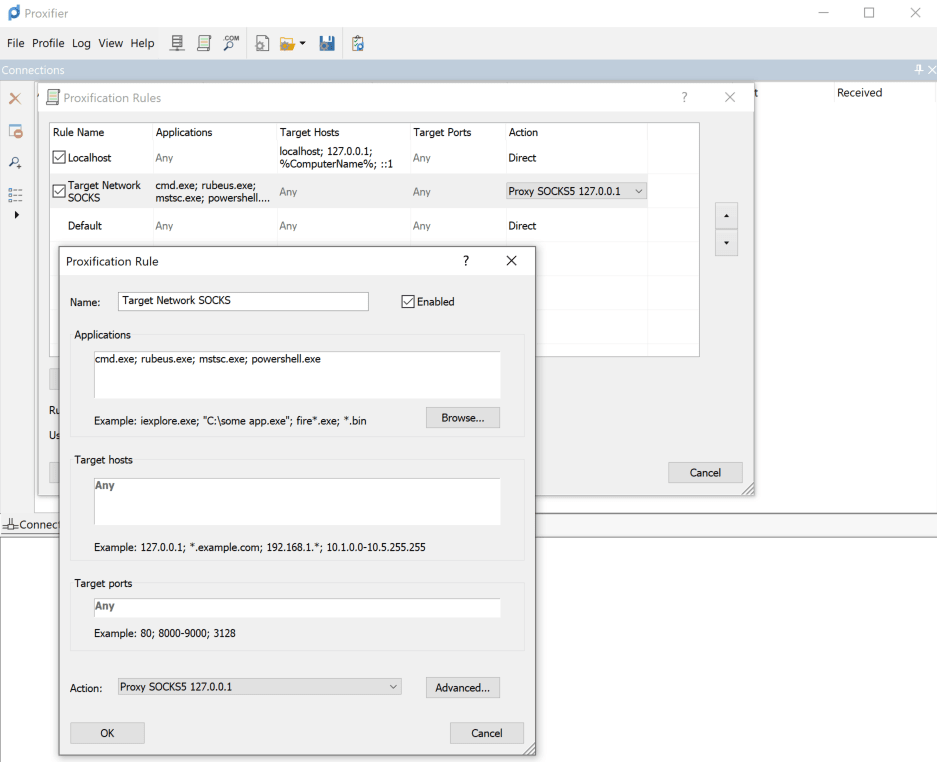
Proxifier rule editor screenshot showing mstsc.exe over SOCKS5 proxy.
Can I hide the server’s IP without changing the RDP client?
Yes. Point a reverse proxy or tunnel at the server instead. TorGuard’s port-forward feature, Cloudflare Tunnel, or an SSH reverse tunnel lets the server dial out to a broker. Clients then hit the broker’s public address and are forwarded inside, so the real host never answers port 3389.
What if I need multi-factor authentication?
A proxy handles transport, not sign-in security. Enable Network Level Authentication on the RDP host, turn on account lockout after five failed attempts, and add Microsoft’s built-in 2FA (or a Duo or Okta plug-in). That layered approach blocks stolen credentials even if someone guesses the proxy exit you’ve allowed.
Conclusion
These answers cover the questions we hear most often. If something still nags you, drop a comment below and we’ll test, tweak, and report back.